

I can’t decide if this is real or an advertisement for the linked article service. I don’t see any CVE in the article which seems to be a good indication of the quality of the content.
I’m not saying that this is misinformation, but I’m extremely sceptical about the nature of this article.




















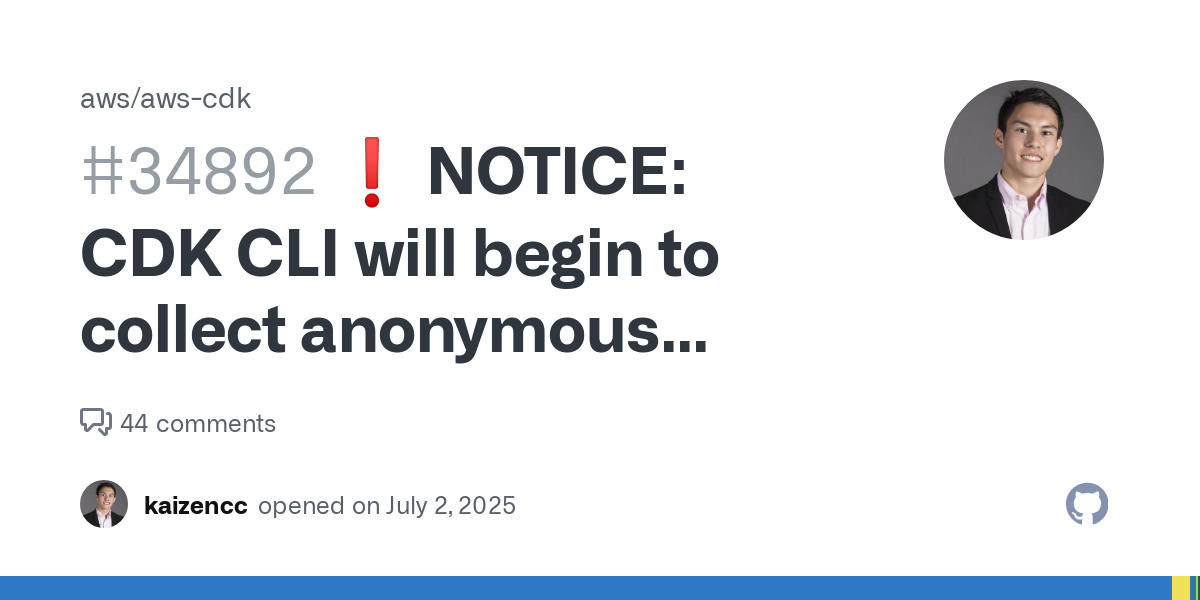
I can’t decide if this is real or an advertisement for the linked article service. I don’t see any CVE in the article which seems to be a good indication of the quality of the content.
I’m not saying that this is misinformation, but I’m extremely sceptical about the nature of this article.